How to remove server_tokens in Azure Application Gateway
Rédigé par uTux Aucun commentaireIn Azure, the Application Gateway is basically a reverse proxy, passing traffic to some backends. While testing the SSL certificate of a listener with ssllabs, I have been surprised by the "HTTP server signature" field: Nexus/2.14.10-01. Indeed, the backend was a Nexus service, but I was expecting to see the server signature of the Application Gateway (which is Nginx), or nothing, but not the backend.
Turns out the HTTP response contains the following header:
< HTTP/1.1 200 OK
< Server: Nexus/2.14.10-01
[...]Many sysadmins and organizations consider this as a security issue, giving attackers information about the server. While I do not totally agree with this statement (Obfuscation), I often disable this information. This is simple with Nginx and Apache, but what about Azure Application Gateway?
Application Gateway -> Your application gateway -> Rewrites -> + Rewrite set
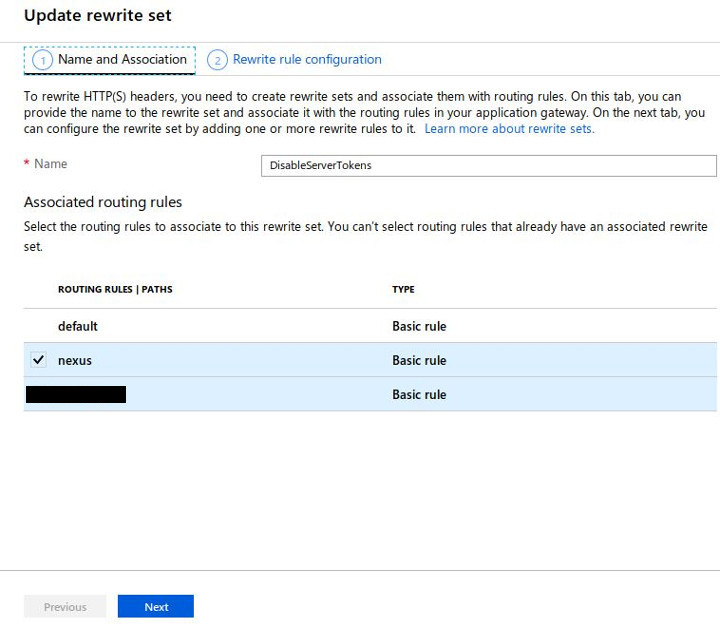
- Name: give a name to your rewrite set. Ie: DisableServerTokens.
- Associated routing rules: Select the rule associated to your backend(s)
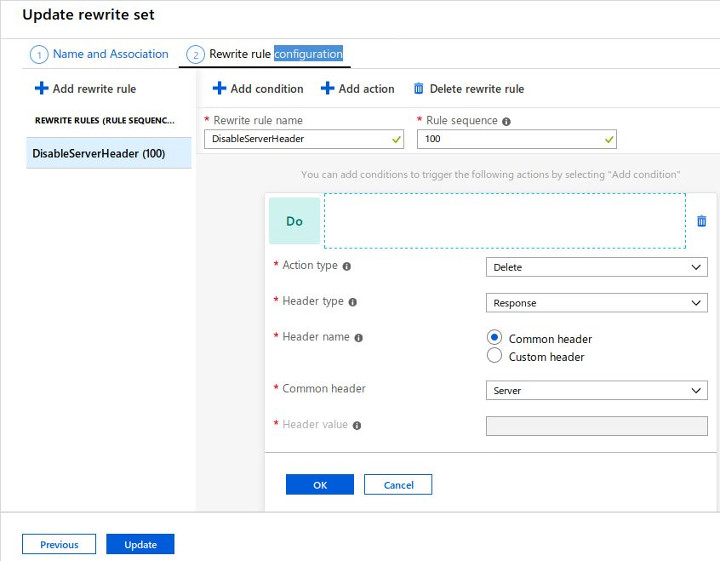
- Rewrite rule name: give a name to your rewrite rule name. Ie: DisableServerHeader.
- Action type: Delete
- Header type: Response
- Header name: Common header
- Common header: Server
Then Save your modifications. This should remove the "Server" HTTP header.